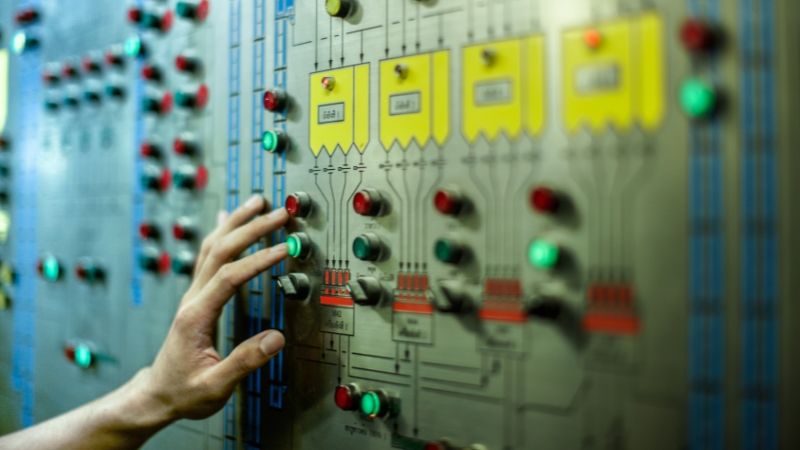
Legacy operational technology (OT) systems are still heavily relied on by much of the industrial and critical infrastructure sectors. As digital transformation becomes the new norm, these legacy systems present complex challenges to implementing vital cybersecurity measures.
The Challenge
Legacy systems may include components that are decades old– meaning their designs never accounted for modern cyberthreats and the implications of digital convergence.
As these systems reach end-of-life (EOL), lack of updates and patches, discontinuation of vendor support, and incompatibilities with emerging tech compound the risk of critical disruption.
Best Practice Solutions
Network Segmentation
By isolating critical systems, you can reduce the spread of cyberattacks and limit the potential impact of security breaches.
Cybersecurity Audits
Regular reviews of cybersecurity policies and controls can identify vulnerabilities, ensure regulatory compliance, and uncover inefficiencies.
Access Control
Enforcing strong authentication, authorization, and accountability mechanisms ensure only the necessary personnel have access to critical systems.
Incident Response Planning
Developing and routinely testing an incident response plan enables the efficient identification and mitigation of cyber incidents.
The Takeaway
Integrating new tech into legacy OT systems can seem daunting, but with an informed understanding of the risks and a commitment to implementing best practices, you can protect your organization’s critical systems and stay competitive in the digital age of industry.
Ready to learn more? Contact us today to schedule a no-cost consultation.
We empower our clients to build safe, sustainable operations by delivering comprehensive Operational Technology (OT) solutions. From concept to implementation and beyond– we'll be there every step of the way.
Let's collaborate.
Schedule a no-cost consultation today.

solution brief
Disaster Recovery
More Posts