Is an Air-Gap “Good Enough” to keep your Industrial Control System secure? Short answer: No. Here’s why…
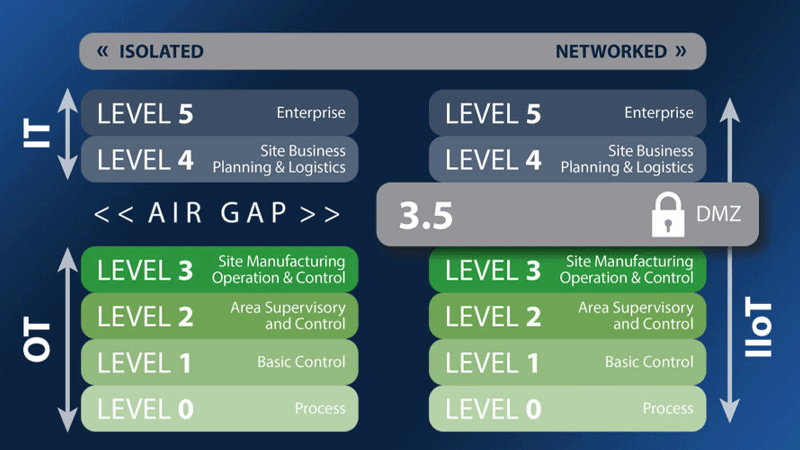
“Security by isolation” or air-gapping previously worked in Operational Technology (OT) environments when OT and IT were completely isolated from one another. Many older systems based on PLC’s and SCADA were built without cybersecurity in mind. OT and IT are now converging as organizations embrace the digital transformation, and security experts are now declaring the air gap dead as security by isolation is not a long-term solution for protecting OT assets.
Air Gapping an OT system has very limited value in today’s constant technological advances. It can no longer be used as a sole security solution in the long term for three reasons:
- It causes organizations to miss out on valuable data.
- It is more costly and difficult for maintenance and repairs.
- It is more prone to security breaches than a “connected” OT system.
Missing out on Data
While air-gapped OT systems can minimize risks, organizations are not able to benefit from the highly valuable data these systems generate. Data analyzed in real time can provide business intelligence to cut costs, reduce downtime, and improve efficiency. These opportunity costs outweigh air-gapping as a viable cyber security measure.
Higher Maintenance Costs
Maintaining air-gapped OT systems are more expensive and difficult because the engineering tools of a connected system cannot be used to perform routine maintenance or troubleshoot problems. It also limits the system from secure remote support by technical experts. Without remote access, facilities experience higher support costs and increased downtime. The reality is that even a properly air-gapped system is not completely protected; Every system is a potential breach target, and even air-gapped systems can be infiltrated. Organizations must engage in active monitoring and security measures to mitigate the risks.
Reduced Security
Air Gaps can be physically breached by a third-party networked laptop, USB drive, removable media, smartphone, or other devices. Allowing OT systems to connect with these devices creates vulnerabilities that air gapping cannot protect against. Air gapping makes it difficult for users to move back and forth between the air-gapped device and network-connected devices. For ease of use, an individual may use an unsecure USB drive to transfer data which could compromise an air-gapped system.
OT infrastructure is only as secure as the user operating the devices. An openly accessible USB port can serve as an entry route for malware. Smartphones provide another convenient route to cross air gaps when switched to Wi-Fi hotspot mode. The Wi-Fi hotspots can also be used as an entry point by hackers or those with ill intentions.
90+% of randomly found USB drives are picked up by the casual person and more than half are plugged into a PC.
Source: Kapersky
Why your OT control systems can’t afford cybersecurity shortcuts:
OT cyber-attacks are more dangerous in nature. An OT attack can pose risks to operational and safety systems, employees, plant, and environment. Because the outcome of an OT cyber-attack is more catastrophic, it is essential that organizations prioritize cybersecurity. While air gapping provides some security, it is not the best option to select in the competitive marketplace.
Air gapped control systems are also more vulnerable because they don’t receive the latest Windows security patches easily, therefore are usually neglected. As new virus threats emerge, the OT system will likely be unprotected, unlike its Enterprise counterpart.
We must accept the fact that air gapping as a security control is no longer a valid option. IT and OT will continue to converge leaving air gapping to be useless. Facilities should take advantage of the opportunities from integrated technologies to reduce costs and downtime while improving efficiency. While doing so, they must prioritize OT security to lessen the risk and still capitalize on the advantages of a connected IT and OT world.
Ready to learn more? Contact us today to schedule a no-cost consultation.
We empower our clients to build safe, sustainable operations by delivering comprehensive Operational Technology (OT) solutions. From concept to implementation and beyond– we'll be there every step of the way.
Let's collaborate.
Schedule a no-cost consultation today.

more on our website
Industrial Cybe
More Posts