Navigating today’s cybersecurity regulations can feel overwhelming, especially in industrial environments where operational realities add complexity.
A compliance assessment cuts through that noise by answering a critical question: are we truly meeting our regulatory requirements?
It’s not just about avoiding fines. It’s about building a structured, auditable security program that aligns with recognized standards and stands up to real-world scrutiny.
A compliance assessment evaluates your organization’s alignment with established frameworks such as ISA/IEC 62443, NIST Cybersecurity Framework (including ICS guidance), and NERC CIP. It compares your existing controls, processes, and documentation against required standards, clearly identifying where you meet expectations and where gaps remain.
Why It Matters in Industrial OT
For industrial organizations, compliance is no longer optional, it’s operationally critical.
Cyber incidents in OT environments don’t just impact data, they can disrupt production, impact safety, and create regulatory exposure. At the same time, evolving mandates (such as MTSA updates and sector-specific regulations) are increasing expectations for demonstrable cybersecurity maturity.
A compliance assessment ensures you are not only prepared for audits but are also building a defensible, resilient security posture. It shifts compliance from a checkbox exercise to a sustainable operational capability.
Key Components
Policy and Documentation Review
We evaluate your existing policies, procedures, and supporting documentation, from incident response to asset management. The goal is to ensure documentation is not only present, but accurate, actionable, and aligned with the target framework.
Technical Control Evaluation
Compliance doesn’t stop at documentation. We validate that technical controls are implemented and functioning as intended, reviewing segmentation, access controls, firewall configurations, and system hardening within the realities of an OT environment.
Regulatory Gap Identification
We perform a structured gap analysis to identify where your current posture diverges from required standards. The output is a clear, actionable roadmap, not just a list of deficiencies.
Remediation Planning
Closing gaps requires more than recommendations. We work alongside your team to prioritize actions based on risk, operational impact, and compliance urgency, balancing security improvements with production continuity.
Making Compliance Practical in OT
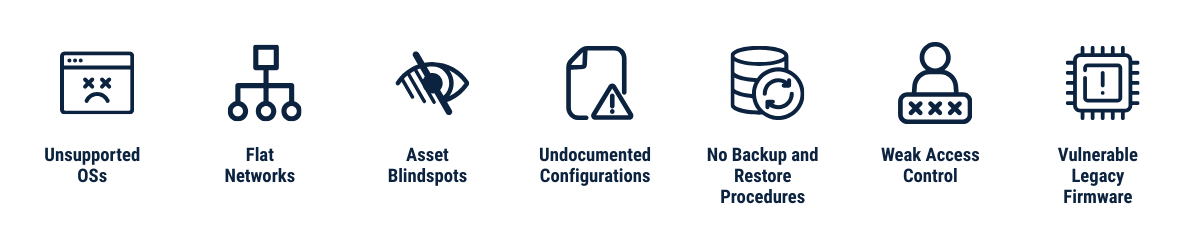
Compliance in OT isn’t always straightforward. Legacy infrastructure, uptime requirements, and safety considerations make traditional IT-driven approaches difficult to apply in practice.
A successful compliance program must account for how industrial systems actually operate, where changes must be carefully planned, validated, and executed without disrupting production.
This is where experience matters. Translating regulatory requirements into real-world implementation, while maintaining operational continuity, is what ultimately determines success.
Key Takeaway
A compliance assessment provides clarity in a complex regulatory landscape. It establishes a defensible baseline, identifies what matters most, and creates a path forward.
Done right, it’s not just about passing an audit, it’s about building a program that is repeatable, sustainable, and aligned with how industrial operations actually run.
Champion brings a practical, execution-focused approach to OT compliance, bridging the gap between regulatory requirements and operational reality.
OT-Native Expertise
Deep experience across control systems, networks, and industrial processes ensures recommendations are grounded in real operations.
Operationally Safe Execution
Solutions are designed and validated with uptime, safety, and production constraints in mind.
End-to-End Support
From assessment through remediation and ongoing support, we stay engaged to ensure outcomes—not just deliverables.
Aligned with Modernization Efforts
Compliance is integrated into broader initiatives such as system upgrades, network redesigns, and cybersecurity improvements.
This approach is demonstrated in real-world projects, such as control system upgrades and network modernization executed without operational disruption, where compliance, reliability, and performance are advanced together.
Ready to learn more? Contact us today to schedule a no-cost consultation.
We empower our clients to build safe, sustainable operations by delivering comprehensive Operational Technology (OT) solutions. From concept to implementation and beyond– we'll be there every step of the way.

Solution Brief
MTSA Cybersecurity Compliance
Let's collaborate.
Schedule a no-cost consultation today.
More Posts




 Optimizing Uptime Through OT Monitoring
Optimizing Uptime Through OT Monitoring Three Pillars of Modern OT Monitoring
Three Pillars of Modern OT Monitoring Why the Blend Matters
Why the Blend Matters